

Note: Please check your Spam or Junk folder, in case you didn't receive the email with verification code.
Linear: Sequential Order
Course overview
According to the Wall Street Journal, “All IT Jobs Are Cybersecurity Jobs Now.” In this course, we examine the concept of Red team – Blue team security professionals. You will practice Red team versus Blue team exercises, where one group of security pros--the red team--attacks some part or parts of a company’s security infrastructure, and an opposing group--the blue team--defends against the attack. Both teams work to strengthen a company’s defenses. You'll learn how both the red and blue teams help the business attain a higher level of security, something the security industry is now calling the Purple team.
Program Structure
1. This course is designed to get you started as quickly as possible. There are a variety of self-paced learning activities.
2. Scored Questions are located at the end of each module to check your general understanding of the key concepts.
3. Videos and Demonstrations are located throughout the course to explain the concepts and provide system walk-throughs.
4. Final Exam: The Final Exam questions are scored and check your understanding of the key concepts in the course.
Program Details
1. Introduction
2. Understanding the Cybersecurity Landscape
3. Red Team Penetration, Lateral Movement,Escalation, and Exfiltration
4. Blue Team Detection, Investigation, Response, and Mitigation
5.Beyond the Breach
Effort or Learning time
16 Hrs
Skills Required
1. An understanding of role s and functions of Security Administrator, System Administrator, or a Network Administrator.
2. Basic knowledge of Networking and security systems.
3. Introductory level knowledge of Active Directory, including functions of a domain control, sign on services, and an understanding of group policy.
Who can learn
Following professionals can take up this courses:
1. Any student undergoing graduation /PG in Computer Science /Technology/Electronics and Electical Engg.
2. Engineering or Non Engineering students aspiring to make career in security systems.
3. Any student/professional with interest in Windows Server administration, maintenance, and troubleshooting.
4. Any student/professional with basic understanding of Windows networking technologies.
 1. Before You Start
1. Before You Start
 Before You Start - transcript
Before You Start - transcript
 2. Hello
2. Hello
 3. Course Syllabus
3. Course Syllabus
 4. Pre-Course Survey
4. Pre-Course Survey
 Assessment
7 Questions
Assessment
7 Questions
 1. Current Cybersecurity Landscape
1. Current Cybersecurity Landscape
 Overview-transcript
Overview-transcript
 Monetization of malware-transcript
Monetization of malware-transcript
 Increasing regulations-transcript
Increasing regulations-transcript
 2. Assume Compromise Philsophy
2. Assume Compromise Philsophy
 Compromise examples-transcript
Compromise examples-transcript
 3 Cost of a breach
3 Cost of a breach
 Overview-transcript
Overview-transcript
 Assessment
8 Questions
Assessment
8 Questions
 1. Red Team versus Blue Team Exercises
1. Red Team versus Blue Team Exercises
 2. The Attacker
2. The Attacker
 Overview-transcript
Overview-transcript
 3. Red Team Kill Chain
3. Red Team Kill Chain
 Overview-transcript
Overview-transcript
 4. Document Vulnerabilities
4. Document Vulnerabilities
 Assessment
9 Questions
Assessment
9 Questions
 1. Blue Team
1. Blue Team
 2. Blue Team Kill Chain
2. Blue Team Kill Chain
 Plan a response-transcript
Plan a response-transcript
 Execute-transcript
Execute-transcript
 3. Restrict Privilege Escalation
3. Restrict Privilege Escalation
 4. Restrict Lateral Movement
4. Restrict Lateral Movement
 Code Integrity policies-transcript
Code Integrity policies-transcript
 5. Attack Detection
5. Attack Detection
 Assessment
5 Questions
Assessment
5 Questions
 1. CIA Triad
1. CIA Triad
 2. Organization Preparations
2. Organization Preparations
 3. Developing and Maintaining Policies
3. Developing and Maintaining Policies
 Assessment
10 Questions
Assessment
10 Questions
 Assessment
24 Questions
Assessment
24 Questions
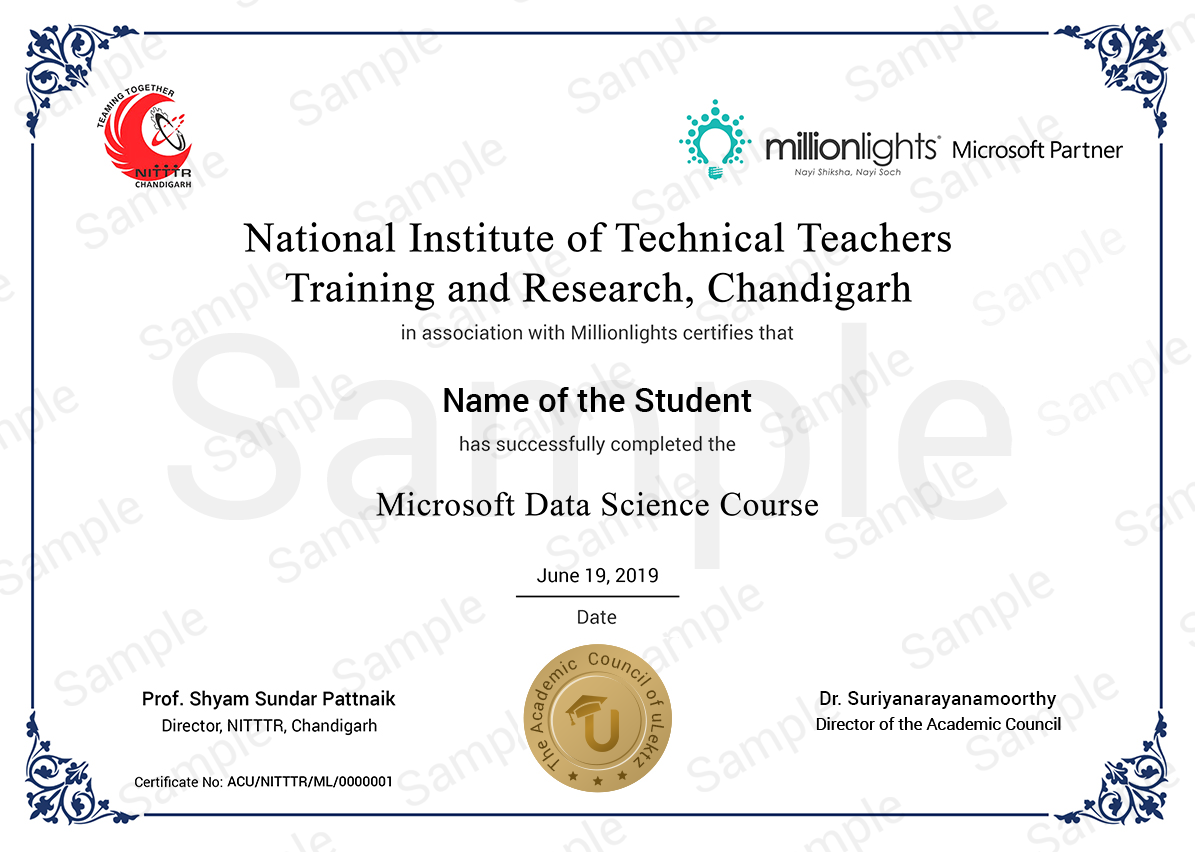
The certificate issued for the Course will have
Only the e-certificate will be made available. No Hard copies. The certificates issued by NITTTR Chandigarh, MHRD - Government of India and Million Lights. can be e-verifiable at www.ulektzskills.com/verify.


 45 hours Learning Content
45 hours Learning Content 100% online Courses
100% online Courses English Language
English Language Certifications
Certifications